Build a Secure Digital Vault and Ready‑to‑Go Emergency Files
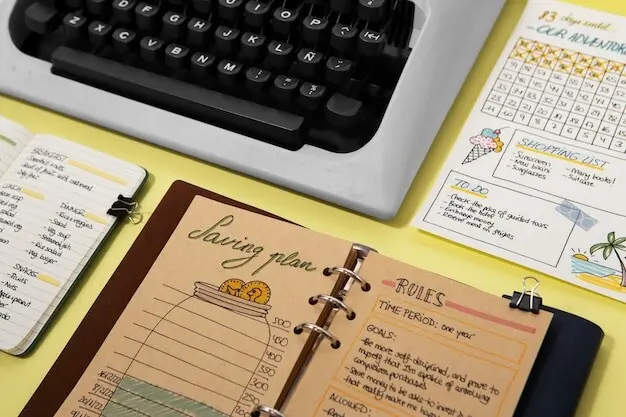
Today we dive into building a secure digital document vault and emergency grab‑and‑go files, so your identity, medical records, policies, and legal papers stay protected yet instantly accessible. You will learn practical steps, proven tools, and resilient habits that safeguard your family, support calm decisions during crises, and make everyday paperwork remarkably easier.
Start With Clarity: What Truly Belongs Inside
Identify Critical Records Without Guesswork
List passports, birth and marriage certificates, Social Security cards, titles and deeds, wills, medical histories, immunizations, prescriptions, insurance policies, tax returns, business documents, and critical photos of assets. Add emergency contacts, logins to vital accounts, and recent utility bills for identity verification. Prioritize anything required to prove ownership, authorize medical care, restore access, or quickly file claims after loss.
Prioritize By Impact, Replaceability, And Time Sensitivity
Classify documents by how hard they are to replace, how urgently you might need them, and how much damage their exposure could cause. A deed is irreplaceable and sensitive, while a gym contract is neither. This triage drives scanning order, backup frequency, access rules, and whether a copy belongs on the grab‑and‑go drive or only in the encrypted primary vault.
Create A Simple, Predictable Taxonomy
Organize by life domain—Identity, Health, Property, Finance, Legal, Work, Education, Family, and Emergency. Within each, use stable folders like Policies, Statements, Certificates, and Receipts. Everyone in your household should understand the structure at a glance, reducing search time, onboarding friction, and mistakes during stressful moments when speed, clarity, and confidence matter most.
Digitize With Precision: Scanning, OCR, And Clean Copies
{{SECTION_SUBTITLE}}
Choose Scanning Standards That Age Gracefully
Use 300–400 DPI for text, 600 DPI for fine print or stamps, and color or grayscale to preserve seals and signatures. Enable de‑skew, de‑speckle, and straight‑edge cropping. Avoid camera shadows by using indirect light or a document mat. The result is a faithful reproduction that future you—and future software—can trust without tedious rescans or compromised readability.

Pick Durable Formats And Enable OCR
Save master copies as PDF/A for long‑term preservation and predictable rendering. Apply OCR to make text selectable and searchable across devices, even offline. For photos of valuables or serial numbers, use high‑quality JPEG or TIFF. Keep scans uncompressed in masters when feasible, then export compressed working copies for speed. Verified text layers dramatically accelerate emergencies, claims, and audits.
Lock It Down: Encryption, Keys, And Access
Strong protection is thoughtful, layered, and humane. We will select proven encryption tools, craft memorable yet robust passphrases, and establish recovery methods that do not sabotage security. The goal is simple: airtight confidentiality without fragile complexity, enabling quick personal access, safe family contingencies, and confident sharing when professionals require proof or permissions during critical moments.

Choose Battle‑Tested Encryption Tools
Prefer audited, widely trusted options: full‑disk encryption on computers, encrypted volumes for archives, and zero‑knowledge cloud vaults for synced access. Use modern ciphers and default secure settings rather than exotic tweaks. Keep software updated and disable legacy protocols. When in doubt, follow vendor hardening guides. Security grows from defaults you will reliably sustain under everyday pressures.
Master Passphrases And Key Management
Create long passphrases using memorable sentences, sprinkled with unique separators. Store credentials in a reputable password manager protected by strong MFA. Print emergency key material on paper sealed in a fire‑resistant envelope, placed in a safe‑deposit box. Avoid sharing secrets via email or chat. Rotate keys after major life events, compromised devices, or suspicious account notifications.
Enable Multifactor And Harden Devices
Turn on MFA everywhere, preferring app or hardware tokens over SMS. Lock screens with timeouts, full‑disk encryption, and biometric unlock for speed. Disable auto‑mount of external drives. Patch promptly, uninstall risky extensions, and restrict admin rights to reduce damage. A secure vault depends on the everyday posture of the laptops and phones that open it.
Resilience By Design: Backups, Redundancy, And Testing
Disasters rarely send calendar invites. A robust backup plan cushions hardware failure, theft, ransomware, and accidental deletion. We will implement the 3‑2‑1‑1‑0 strategy, test restores regularly, and verify file integrity with checksums, so your vault and grab‑and‑go copies recover predictably, complete, and uncompromised when the stakes are highest and stress clouds judgment.
Ready In Minutes: The Grab‑And‑Go Kit
When evacuation orders arrive, you should not be wrestling zip files. Prepare a small encrypted SSD or USB key with selective, high‑value copies plus a few printed essentials in a waterproof sleeve. Clear labels, lightweight redundancy, and a practiced checklist transform chaotic departures into confident action, protecting identity, medicine access, cash flow, and smooth reentry to normal life.
Include identity scans, insurance cards, property records, recent photos of rooms and valuables, critical medical summaries, prescriptions, and contact sheets. Store on an encrypted drive with a distinct passphrase from your main vault. Add printed phone numbers for doctors, insurers, and banks. Keep the kit near the exit, alongside copies of keys, spare glasses, and a compact power bank.
List five fast steps: grab encrypted drive, grab printed packet, confirm wallets and meds, snap current home photos, lock windows and water. Add tiny boxes to tick during adrenaline‑heavy moments. During a winter pipe burst, one reader executed this list and filed an insurance claim within hours, surprising the adjuster with precise documentation and serene confidence despite the chaos.
Walk through the kit together twice a year. Confirm who knows the vault’s emergency passphrase handoff, and store sealed instructions with a lawyer or safe‑deposit box. Practice on a weeknight, timing each step. Familiarity breeds calm, reducing mistakes when you least expect interruption, whether wildfire smoke, sudden hospitalization, or a cross‑country call demanding instant proof of authorization.


Set A Sustainable Update Rhythm
Adopt monthly quick sweeps and quarterly deep refreshes. Replace expired IDs, add new statements, archive duplicates, and remove obsolete versions. Tie reviews to tax season, open enrollment, and policy renewals. A short recurring appointment prevents backlog, trims anxiety, and keeps your system light enough that you will actually use it, not admire it once and forget.

Audit Access And Change History
Log who can open what, on which devices, and why. Review sharing links, emergency access designations, and delegated rights after job changes, moves, or breakups. Enable alerts for unusual sign‑ins. Keep a minimal, signed paper copy of recovery instructions offline. Transparent accountability prevents accidental oversharing and equips loved ones to help when assistance is needed quickly and safely.
All Rights Reserved.